Beyond the Usual Suspects: Understanding Today's Evolving Cyber Adversaries
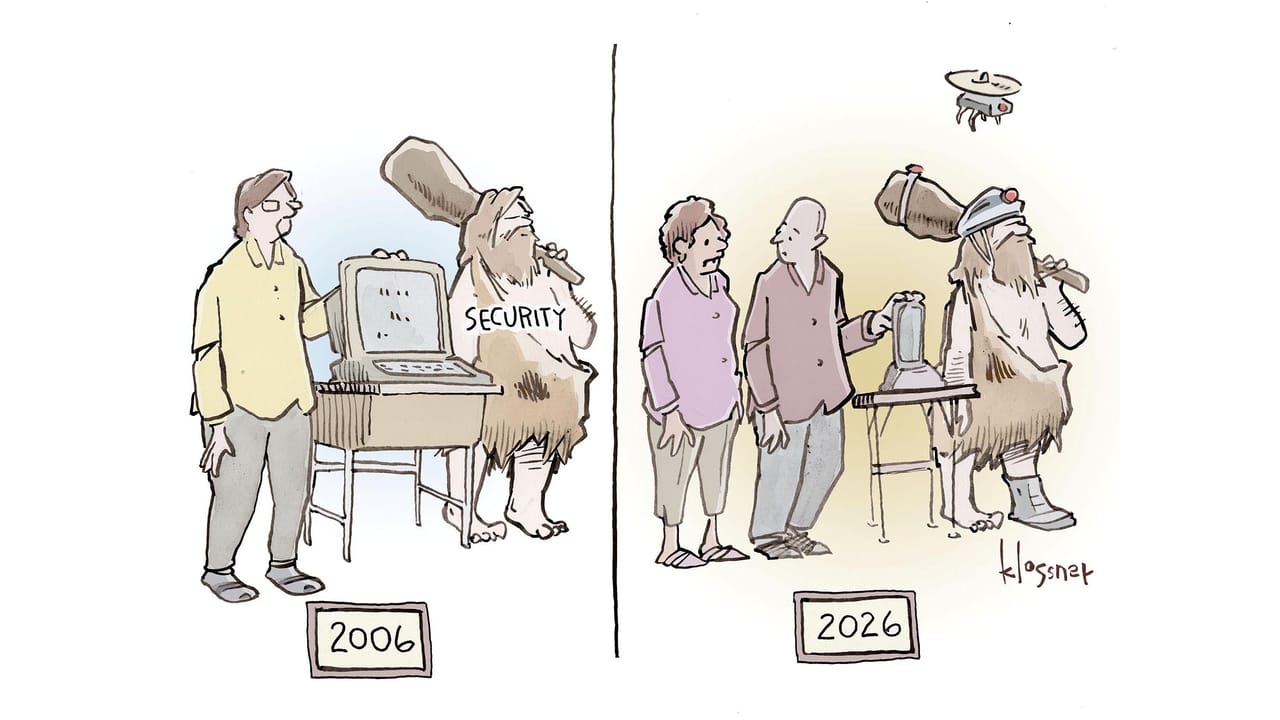
Cyber threats are no longer just about lone hackers or nation-states; the landscape now includes mercenary groups and even security firms gone rogue. Understanding these new adversary profiles is crucial for SMBs to build effective defenses.
Jordan Kim
Staff Writer
For small and medium-sized businesses (SMBs), the cybersecurity threat landscape often feels like a constant battle against familiar foes: ransomware gangs, phishing scams, and data breaches. While these remain critical concerns, recent developments highlight a more complex and diversified adversary ecosystem. It's no longer just about the lone hacker or the well-funded nation-state; new players, from mercenary cyber groups to rogue security firms, are reshaping how and why attacks occur. Understanding these evolving adversary profiles is essential for building resilient defenses.
The Rise of Cyber Mercenaries and Geopolitical Proxies
The line between financially motivated cybercrime and politically motivated attacks is blurring. We're seeing an increase in financially driven groups offering their services to state actors or engaging in politically charged attacks for their own gain. This means an SMB could become collateral damage in a geopolitical conflict, even if they have no direct ties to the involved parties.
These groups often operate with sophisticated tools and techniques, previously reserved for advanced persistent threats (APTs). Their motivation might be financial, but their targets can be dictated by a client's geopolitical agenda. This adds a layer of unpredictability to threat modeling, as your business could be targeted not for its data, but for its perceived association or critical infrastructure role in a broader conflict.
The Double-Edged Sword: When Security Firms Go Rogue
Perhaps one of the most unsettling developments is the emergence of security firms or individuals within them actively participating in malicious activities. The idea that a company specializing in protection could be weaponizing its knowledge against others is a significant trust erosion. This isn't just about insider threats; it's about organizations whose core business is security becoming the very source of attacks.
This trend underscores the importance of scrutinizing every vendor, even those in the security space. It also highlights the potential for sophisticated, targeted attacks that leverage deep knowledge of defensive mechanisms. For SMBs, this means that even trusted partners could, in rare and extreme cases, become a vector for compromise, making due diligence more critical than ever.
Supply Chain Attacks: A Broader Attack Surface
Software supply chain attacks continue to be a potent vector for adversaries. These attacks leverage trusted software components or development processes to inject malicious code, often with a delayed payload. Recent incidents involving poisoned open-source libraries like Ruby Gems and Go Modules demonstrate how attackers are exploiting the very infrastructure that modern businesses rely on for efficiency.
These aren't random acts; they are often carefully planned campaigns designed to achieve credential theft, system tampering, or data exfiltration. The challenge for SMBs is that the compromise often happens upstream, within a vendor's development pipeline or a widely used open-source project. This makes detection difficult, as the malicious code might initially appear legitimate.
Practical Takeaways for SMB Decision-Makers
Navigating this complex threat landscape requires a proactive and informed approach. Here's how SMBs can adapt their cybersecurity strategies:
- Enhance Vendor Due Diligence: Go beyond basic security questionnaires. For all third-party software and services, especially security providers, inquire about their internal security practices, incident response plans, and employee vetting. Understand their supply chain risks. Consider independent security audits or certifications.
- Strengthen Supply Chain Security: Implement policies for using open-source components. Utilize software composition analysis (SCA) tools to identify known vulnerabilities and malicious packages in your dependencies. Monitor for new versions and promptly apply updates.
- Implement Zero Trust Principles: Assume no user, device, or application can be trusted by default, regardless of whether they are inside or outside your network perimeter. Verify everything. This significantly limits the impact of compromised credentials or rogue internal actors.
- Segment Your Network: Isolate critical systems and data from less sensitive parts of your network. If one segment is compromised, the attacker's ability to move laterally and access high-value assets is severely restricted.
- Invest in Advanced Threat Detection: Traditional antivirus is no longer sufficient. Consider Endpoint Detection and Response (EDR) or Managed Detection and Response (MDR) services. These tools and services can identify anomalous behavior and sophisticated attacks that bypass signature-based defenses.
- Regularly Review Access Controls: Ensure that employees only have access to the resources absolutely necessary for their roles (least privilege principle). Regularly audit and revoke access for former employees or those with changed responsibilities.
- Develop a Robust Incident Response Plan: Understand that a breach is a matter of when, not if. Have a clear, tested plan for detecting, responding to, and recovering from a cyberattack. This includes communication strategies, forensic analysis, and data recovery procedures.
Bottom Line
The cybersecurity landscape is dynamic, with new adversary types and attack vectors constantly emerging. SMBs can no longer afford to focus solely on traditional threats. By understanding the motivations and methods of cyber mercenaries, guarding against rogue security actors, and fortifying their software supply chain, SMBs can build more robust and resilient defenses. Proactive due diligence, a zero-trust mindset, and advanced detection capabilities are no longer luxuries; they are necessities for surviving in today's complex digital environment.
Topics