Beyond Your Network: Managing Third-Party Cyber Risk for SMBs
Your cybersecurity is only as strong as your weakest link, and often that link lies outside your direct control. Learn how to identify, assess, and mitigate the cyber risks introduced by your vendors and partners.
Alex Rivera
Staff Writer
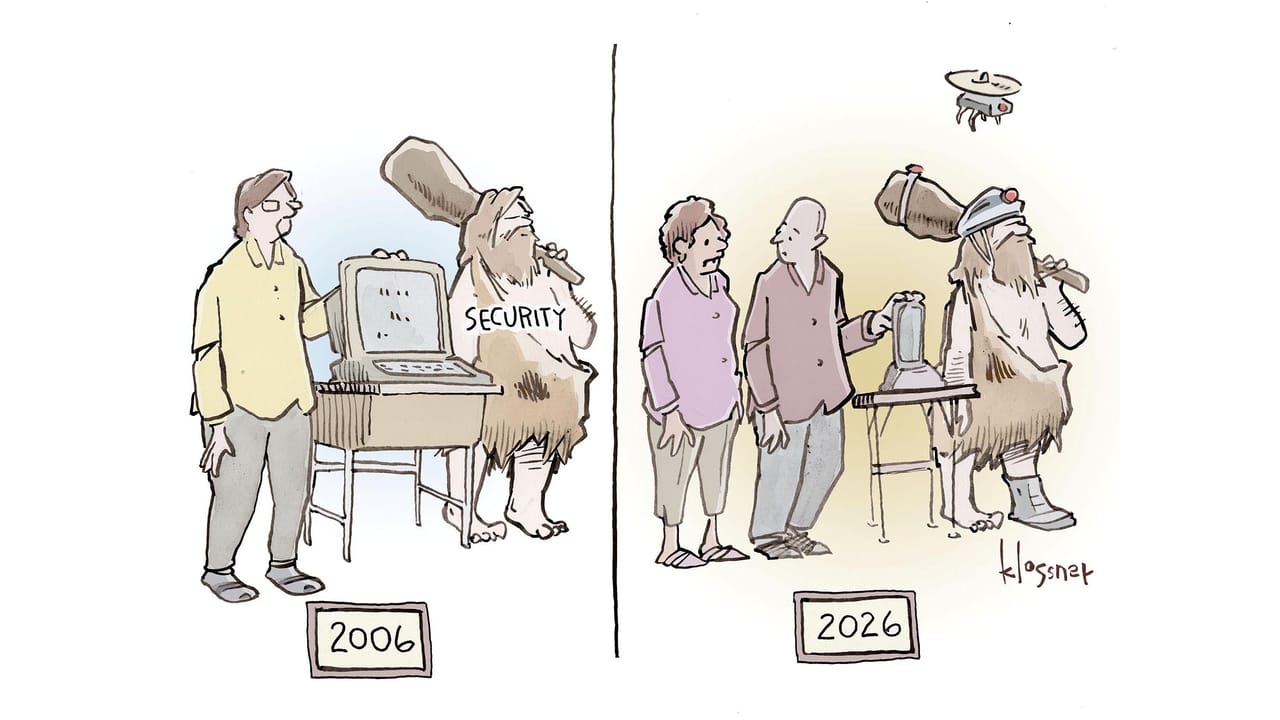
For many small and medium businesses, the focus of cybersecurity remains firmly on internal networks and systems. Firewalls, endpoint protection, and employee training are critical, but they only tell half the story. In today's interconnected digital landscape, your organization's security posture is increasingly defined by the security of your third-party vendors, partners, and even customers. From cloud service providers to payment processors, every external entity with access to your data or systems represents a potential vulnerability.
Recent events underscore this reality. While headlines often focus on large-scale breaches, the underlying mechanisms – compromised systems, supply chain weaknesses, and even insider threats from external parties – are equally relevant to SMBs. Ignoring these external dependencies is no longer an option; it's a significant business risk.
Understanding the Third-Party Risk Landscape
Third-party cyber risk refers to the potential for a security incident originating from an external entity that has access to your organization's sensitive data, systems, or intellectual property. This isn't just about direct data breaches; it includes operational disruptions, reputational damage, and regulatory penalties.
Consider the breadth of your third-party relationships. This includes SaaS providers, managed service providers (MSPs), payment gateways, marketing agencies, HR platforms, and even physical security vendors with network access. Each represents a potential entry point for attackers, especially if their security practices are weaker than your own.
Identifying Your Critical Third-Party Dependencies
The first step in managing third-party risk is to understand who your third parties are and what access they have. This isn't just about listing vendors; it's about mapping data flows and access permissions.
- Inventory All Vendors: Create a comprehensive list of every external company that interacts with your business, regardless of size or service. Don't forget those 'minor' services that might still hold sensitive employee or customer data.
- Map Data and System Access: For each vendor, document what type of data they handle (e.g., PII, financial, intellectual property), where it's stored, and what systems they can access. Categorize vendors based on the criticality and sensitivity of this access.
- Assess Impact: Determine the potential business impact if a specific vendor were to suffer a cyberattack. This helps prioritize your risk management efforts. A vendor handling your payroll data, for instance, presents a higher impact risk than one managing your office plant delivery.
Assessing Vendor Security Posture
Once you know who your critical vendors are, the next step is to evaluate their security practices. This requires a proactive approach, not just assuming they meet your standards.
- Security Questionnaires: Develop a standardized questionnaire for vendors, asking about their security policies, incident response plans, data encryption practices, employee training, and compliance certifications (e.g., SOC 2, ISO 27001). For critical vendors, this should be a mandatory part of onboarding and regular review.
- Contractual Obligations: Ensure your contracts with vendors explicitly outline their cybersecurity responsibilities. This should include data protection clauses, incident notification requirements, audit rights, and liability provisions. Consult legal counsel to ensure these are enforceable.
- Due Diligence and Audits: For high-risk vendors, consider requesting proof of security controls, such as penetration test results or independent audit reports. For very critical relationships, an on-site audit or a third-party security assessment might be warranted.
- Continuous Monitoring: Vendor security isn't a one-time check. Their posture can change. Utilize tools or services that provide continuous monitoring of vendor security ratings or public breach disclosures. This allows you to react quickly to emerging risks.
Mitigating and Managing Third-Party Risks
Identifying and assessing risks is only valuable if followed by mitigation strategies. This involves a combination of technical controls, policy, and ongoing communication.
- Least Privilege Access: Ensure vendors only have the minimum access necessary to perform their services. Regularly review and revoke access that is no longer needed. This applies to both system access and data access.
- Strong Authentication: Mandate multi-factor authentication (MFA) for all vendor access to your systems. This significantly reduces the risk of credential compromise.
- Data Minimization: Only share the absolute minimum amount of data required for a vendor to perform their service. If they don't need access to full customer records, provide anonymized or aggregated data instead.
- Incident Response Integration: Your incident response plan should account for third-party breaches. Establish clear communication protocols with critical vendors for reporting and responding to security incidents that affect shared data or systems.
- Regular Reviews and Re-assessments: Security postures evolve. Schedule annual or bi-annual reviews of critical vendor contracts, security questionnaires, and access permissions. This ensures continued alignment with your risk tolerance.
- Exit Strategy: Plan for what happens when a vendor relationship ends. Ensure there are clear protocols for data return or secure deletion, and for revoking all access rights promptly.
The Cost of Inaction
Neglecting third-party risk can lead to significant financial and reputational damage. A breach originating from a vendor can be just as devastating as an internal one, if not more so, as it often involves data you've entrusted to another party.
Beyond direct financial losses from a breach, there are regulatory fines (e.g., GDPR, CCPA), legal fees, and the cost of rebuilding customer trust. The recent sentencing of individuals for aiding ransomware gangs highlights the serious legal consequences for those involved in cybercrime, which can extend to organizations that fail to protect data entrusted to them by others.
Bottom Line
Your SMB's digital perimeter extends far beyond your office walls. Effective third-party risk management is no longer a luxury; it's a fundamental component of a robust cybersecurity strategy. Start by comprehensively inventorying your vendors and their access. Systematically assess their security controls through questionnaires and contractual agreements. Finally, implement continuous monitoring and strict access controls. Proactively managing these external dependencies will significantly strengthen your overall security posture, protect your data, and safeguard your business reputation in an increasingly interconnected world.
Topics
About the Author
Alex Rivera
Staff Writer · SMB Tech Hub
Our cybersecurity team covers SMB threat prevention, compliance frameworks, and security tool reviews — written for IT managers and business owners who need practical guidance, not enterprise-level jargon.