Beyond the Breach: Fortifying Your SMB's Digital Defenses with Proactive Scanning
Data breaches and ransomware continue to plague businesses, often exploiting known vulnerabilities. Proactive security scanning is no longer optional for SMBs; it's a critical defense.
Alex Rivera
Staff Writer
The headlines are relentless: massive data breaches exposing millions of records, ransomware attacks crippling operations, and even cybersecurity professionals facing jail time for complicity. For small and medium-sized businesses (SMBs), these stories aren't just news; they're stark reminders of the ever-present threats to their digital assets and reputation. While it's easy to feel overwhelmed, the underlying message is clear: proactive defense, particularly through robust security scanning, is no longer a luxury but a fundamental requirement for survival.
Recent incidents underscore this urgency. A student loan breach exposed millions, likely due to exploitable weaknesses in their systems. Simultaneously, the sentencing of individuals involved in BlackCat ransomware attacks highlights the severe consequences for those who facilitate cybercrime, reinforcing the need for SMBs to build impenetrable defenses. Even a decade-old Linux bug, recently rediscovered with AI-assisted scanning, proves that seemingly minor vulnerabilities can persist and be exploited if not systematically identified and patched. This article will guide SMB decision-makers through the essential role of security scanning in preventing such incidents.
Why Proactive Security Scanning is Non-Negotiable for SMBs
Many SMBs operate under the misconception that they are too small to be targets. This is a dangerous myth. Cybercriminals often view SMBs as easier targets with less robust defenses, making them attractive entry points to larger supply chains or direct sources of valuable data. Proactive security scanning helps you identify and mitigate weaknesses before attackers can exploit them.
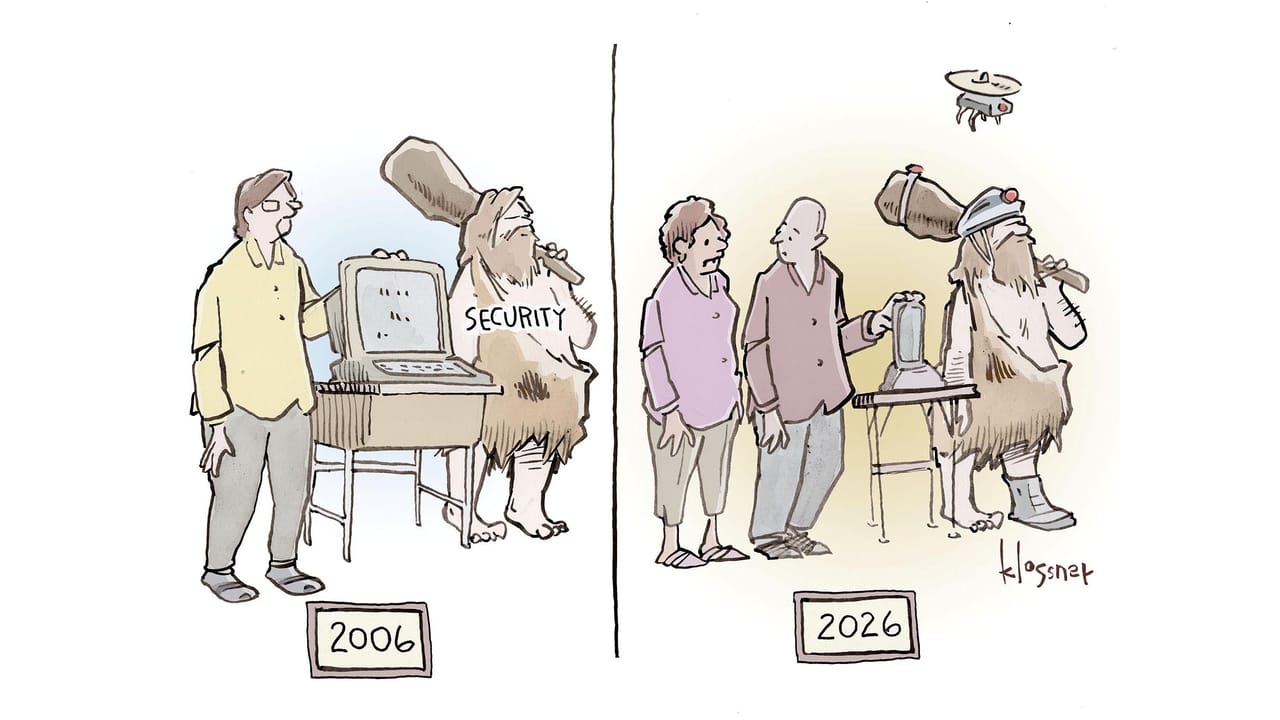
Think of security scanning as a regular health check-up for your digital infrastructure. It systematically probes your systems, networks, and applications for known vulnerabilities, misconfigurations, and other security flaws. Ignoring these checks is akin to ignoring a persistent cough – it might be nothing, or it could be a symptom of something far more serious.
Understanding Key Types of Security Scans
Not all security scans are created equal. Different types target different aspects of your digital ecosystem, providing a comprehensive view of your security posture. Implementing a layered approach using various scanning methods is crucial for robust defense.
1. Vulnerability Scanners
Vulnerability scanners are automated tools that identify known security weaknesses in your operating systems, applications, and network devices. They compare your system configurations and software versions against databases of known vulnerabilities (CVEs – Common Vulnerabilities and Exposures).
- Practical Takeaway: Implement regular, scheduled vulnerability scans across all your internal and external-facing systems. Tools like Nessus, OpenVAS, or Qualys can provide detailed reports. Prioritize patching critical and high-severity vulnerabilities immediately. Don't forget to scan network devices like routers and firewalls.
2. Penetration Testing (Pen Testing)
While vulnerability scans identify *potential* weaknesses, penetration testing goes a step further. It simulates a real-world cyberattack, with ethical hackers attempting to exploit identified vulnerabilities to gain unauthorized access or disrupt services. This provides a realistic assessment of your defenses.
- Practical Takeaway: Engage a reputable third-party security firm for annual or bi-annual penetration tests, especially for critical systems and applications. This provides an objective view of your security posture and helps uncover complex vulnerabilities that automated scanners might miss. Ensure the scope of the test is clearly defined and includes both internal and external assets.
3. Web Application Scanners
If your SMB uses web applications (e.g., customer portals, e-commerce sites, internal dashboards), these are prime targets for attackers. Web application scanners look for common web-specific vulnerabilities like SQL injection, cross-site scripting (XSS), and broken authentication.
- Practical Takeaway: Integrate web application scanning into your development lifecycle if you build your own applications, or use tools like Acunetix, Burp Suite (professional version), or OWASP ZAP for regular scans of your deployed web apps. Pay particular attention to applications that handle sensitive customer data.
4. Cloud Security Posture Management (CSPM) Tools
For SMBs leveraging cloud services (AWS, Azure, Google Cloud), CSPM tools are essential. They continuously monitor your cloud environments for misconfigurations, compliance violations, and security risks that could expose data or lead to unauthorized access.
- Practical Takeaway: If your infrastructure is in the cloud, invest in a CSPM solution. Many cloud providers offer native tools, or you can use third-party options like Wiz or Lacework. These tools help ensure your cloud resources adhere to security best practices and regulatory requirements.
Implementing a Robust Scanning Strategy
Effective security scanning isn't just about running tools; it's about integrating them into a continuous security program. A one-off scan provides only a snapshot; ongoing vigilance is key.
Establish a Regular Schedule
Automate scans to run frequently – daily for critical systems, weekly or monthly for others. The digital landscape changes rapidly, with new vulnerabilities discovered constantly. Regular scanning ensures you catch new issues quickly.
Prioritize and Remediate
Scanning tools will generate numerous findings. Not all vulnerabilities are equally critical. Focus on high-severity issues first, especially those that are externally facing or could lead to data breaches. Develop a clear remediation process with assigned responsibilities and timelines.
Integrate with Patch Management
Scanning identifies vulnerabilities; patch management fixes them. Ensure your scanning results feed directly into your patch management process. This closes the loop, verifying that identified weaknesses are addressed and re-scanned to confirm remediation.
Don't Forget Employee Education
While technical scans are vital, the human element remains a significant vulnerability. Regular security awareness training for employees, covering phishing, strong passwords, and safe browsing habits, complements your technical defenses. Even the most sophisticated scanning won't protect against a successful phishing attack that compromises credentials.
Costs and Considerations for SMBs
Security scanning tools and services come at various price points. Open-source options like OpenVAS can be cost-effective for smaller budgets, though they require more in-house expertise to configure and manage. Commercial solutions offer more features, better support, and often more user-friendly interfaces, but at a higher cost.
Consider the total cost of ownership, including licensing, implementation, and the personnel required to interpret results and perform remediation. For SMBs with limited internal IT security staff, partnering with a Managed Security Service Provider (MSSP) that offers scanning and vulnerability management as part of their services can be a highly effective and efficient solution.
Bottom Line
The recent news of large-scale breaches and criminal convictions serves as a stark reminder: cybersecurity is not a reactive measure. For SMBs, a proactive approach centered on comprehensive security scanning is indispensable. By regularly scanning your systems, networks, and applications for vulnerabilities, performing penetration tests, and integrating these findings into a robust remediation process, you significantly reduce your attack surface.
Invest in the right tools, establish clear processes, and prioritize remediation. This continuous cycle of identification, assessment, and mitigation is your best defense against the evolving threat landscape. Don't wait for a breach to discover your weaknesses; find them first and fix them.
Topics
About the Author
Alex Rivera
Staff Writer · SMB Tech Hub
Our cybersecurity team covers SMB threat prevention, compliance frameworks, and security tool reviews — written for IT managers and business owners who need practical guidance, not enterprise-level jargon.