Beyond the Headlines: Demystifying Cyber Incident Response for SMBs
Recent cyberattacks highlight the critical need for SMBs to have a robust incident response plan. This guide demystifies the process, offering practical steps to prepare for, contain, and recover from a security breach.
James Whitfield
Staff Writer
News headlines frequently report on significant cyber incidents, from nation-state-backed wiper attacks on global corporations to widespread data breaches affecting millions. While these stories often focus on large enterprises, they carry a stark message for small and medium-sized businesses (SMBs): a cyberattack isn't a matter of *if*, but *when*. The impact on an SMB can be devastating, leading to financial losses, reputational damage, and operational paralysis. Having a well-defined incident response plan isn't just good practice; it's essential for survival.
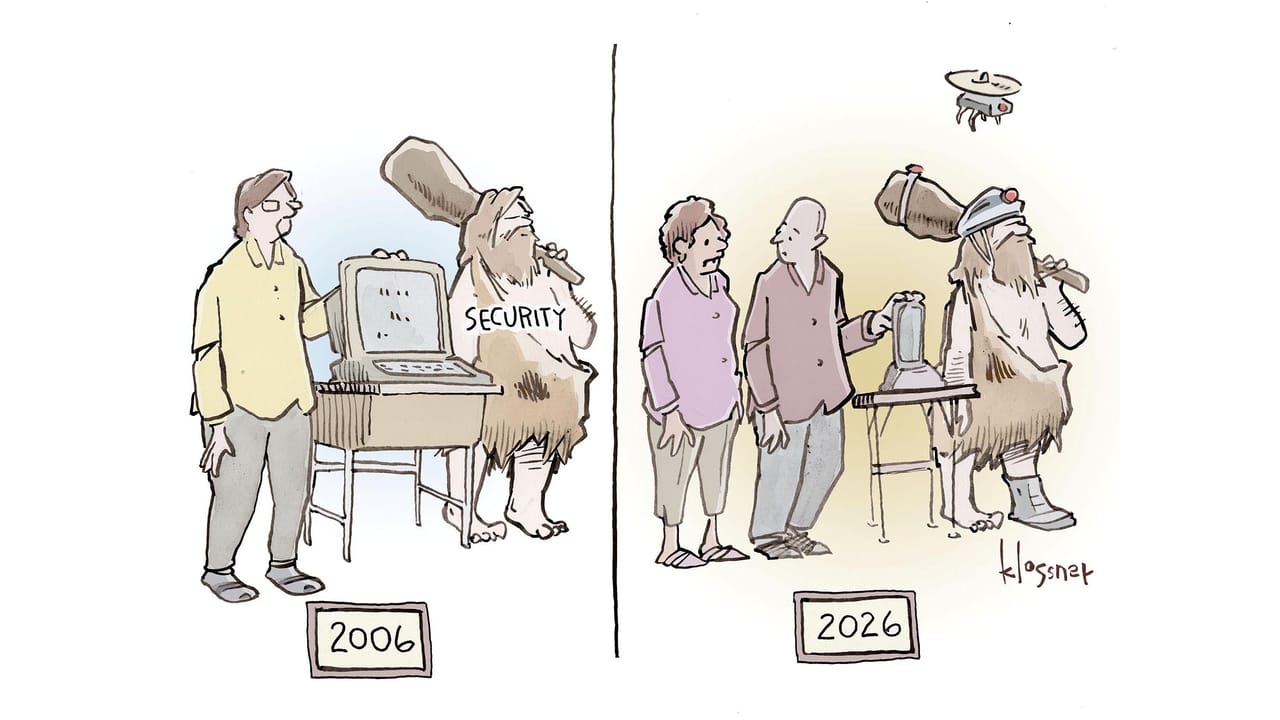
Many SMBs operate under the misconception that they are too small to be targets. This couldn't be further from the truth. Cybercriminals often view SMBs as easier targets with weaker defenses, or as stepping stones to larger supply chain attacks. The recent news of varied threats, from sophisticated wiper attacks to widespread scam texts and even reconnaissance probes, underscores the diverse and relentless nature of current cyber risks. This article will demystify cyber incident response, breaking down the process into actionable steps that SMBs can implement to build resilience.
Why Your SMB Needs a Formal Incident Response Plan (IRP)
An Incident Response Plan (IRP) is your business's blueprint for reacting to and recovering from a cyberattack. Without one, your team will likely respond chaotically, prolonging downtime, increasing costs, and potentially exacerbating the damage. A formal IRP provides clarity, assigns roles, and dictates procedures, ensuring a structured and efficient response.
Consider the implications of a data-wiping attack, like those seen against larger firms. For an SMB, such an event could mean the complete loss of critical business data, customer information, and operational systems. Without a plan, the scramble to restore operations can take weeks or months, potentially leading to business failure. An IRP minimizes this chaos, allowing your team to act decisively under pressure.
Key Phases of an Effective Incident Response Plan
While specific steps may vary, most effective IRPs follow a structured lifecycle. Understanding these phases is crucial for building a plan that works for your business.
1. Preparation: Building Your Cybersecurity Foundation
Preparation is the most critical phase, yet often the most overlooked. It involves establishing the necessary policies, tools, and training *before* an incident occurs. This isn't just about technical safeguards; it's about building a culture of readiness.
- Develop a Written IRP: Document roles, responsibilities, communication protocols, and escalation paths. This isn't a static document; review and update it regularly.
- Form an Incident Response Team: Identify key personnel from IT, legal, HR, communications, and management. Assign specific roles and ensure everyone understands their part.
- Conduct Regular Backups: Implement a robust backup strategy, ensuring critical data is regularly backed up, immutable, and stored off-site. Test restoration processes frequently.
- Implement Security Tools: Deploy essential tools like Endpoint Detection and Response (EDR), firewalls, intrusion detection systems, and email filtering. Ensure they are configured correctly and updated.
- Employee Training: Conduct regular cybersecurity awareness training. Employees are often the first line of defense; they need to recognize phishing attempts, suspicious links, and social engineering tactics.
- Network Segmentation: Divide your network into smaller, isolated segments. This limits the lateral movement of attackers, containing breaches to smaller areas.
- Vendor Agreements: Review contracts with third-party vendors (e.g., cloud providers, managed service providers) to understand their incident response capabilities and your responsibilities.
2. Identification: Detecting and Confirming the Breach
This phase focuses on detecting anomalies and confirming whether a security incident has occurred. Early detection is paramount to minimizing damage.
- Monitor Logs and Alerts: Regularly review logs from firewalls, servers, applications, and security tools. Implement automated alerts for suspicious activities.
- Establish Baselines: Understand what
Topics
About the Author
James Whitfield
Staff Writer · SMB Tech Hub
Our cybersecurity team covers SMB threat prevention, compliance frameworks, and security tool reviews — written for IT managers and business owners who need practical guidance, not enterprise-level jargon.